Flutter apps are a little bit different and hard to bypass ssl pinning.There are many method to bypass ssl pinning for flutter apps and I’m gonna show you one of the method to bypass ssl pinning using reflutter flamework.
This framework helps with Flutter apps reverse engineering using the patched version of the Flutter library which is already compiled and ready for app repacking. This library has snapshot deserialization process modified to allow you perform dynamic analysis.
Installation
pip3 install reflutter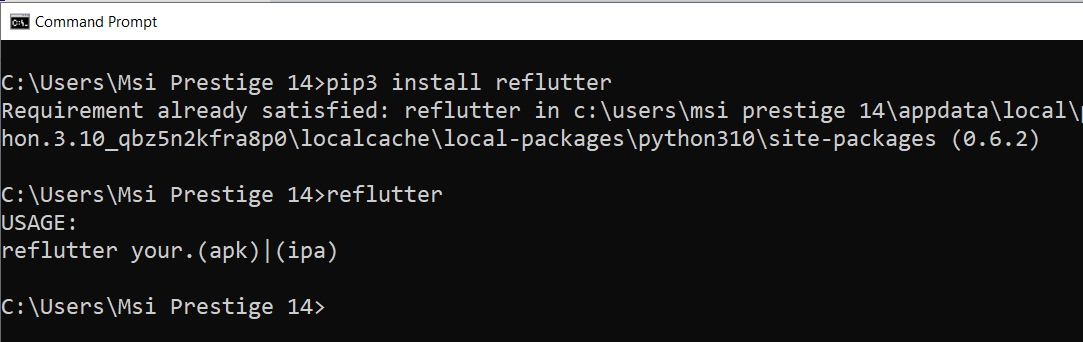
Here is the flutter apps to test
https://github.com/thedarksource/Android/tree/master/flutter-test-apps
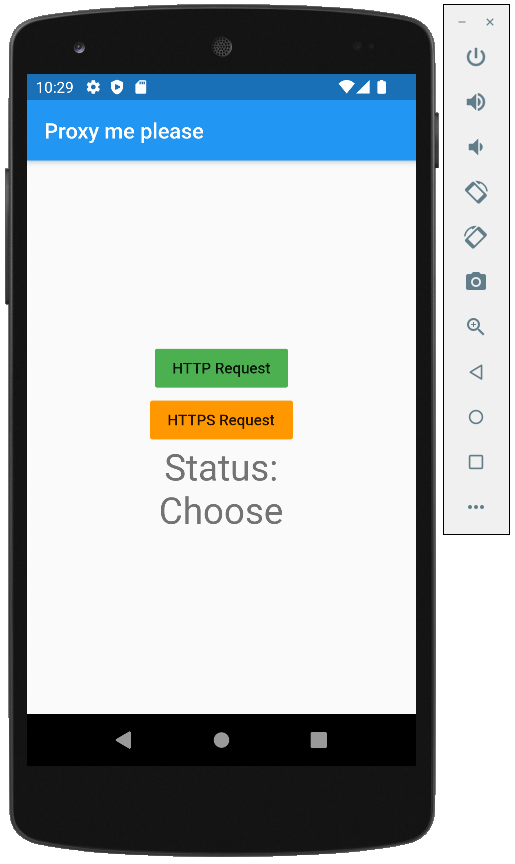
We have two type of requests HTTP and HTTPS , First let’s check HTTP Request.
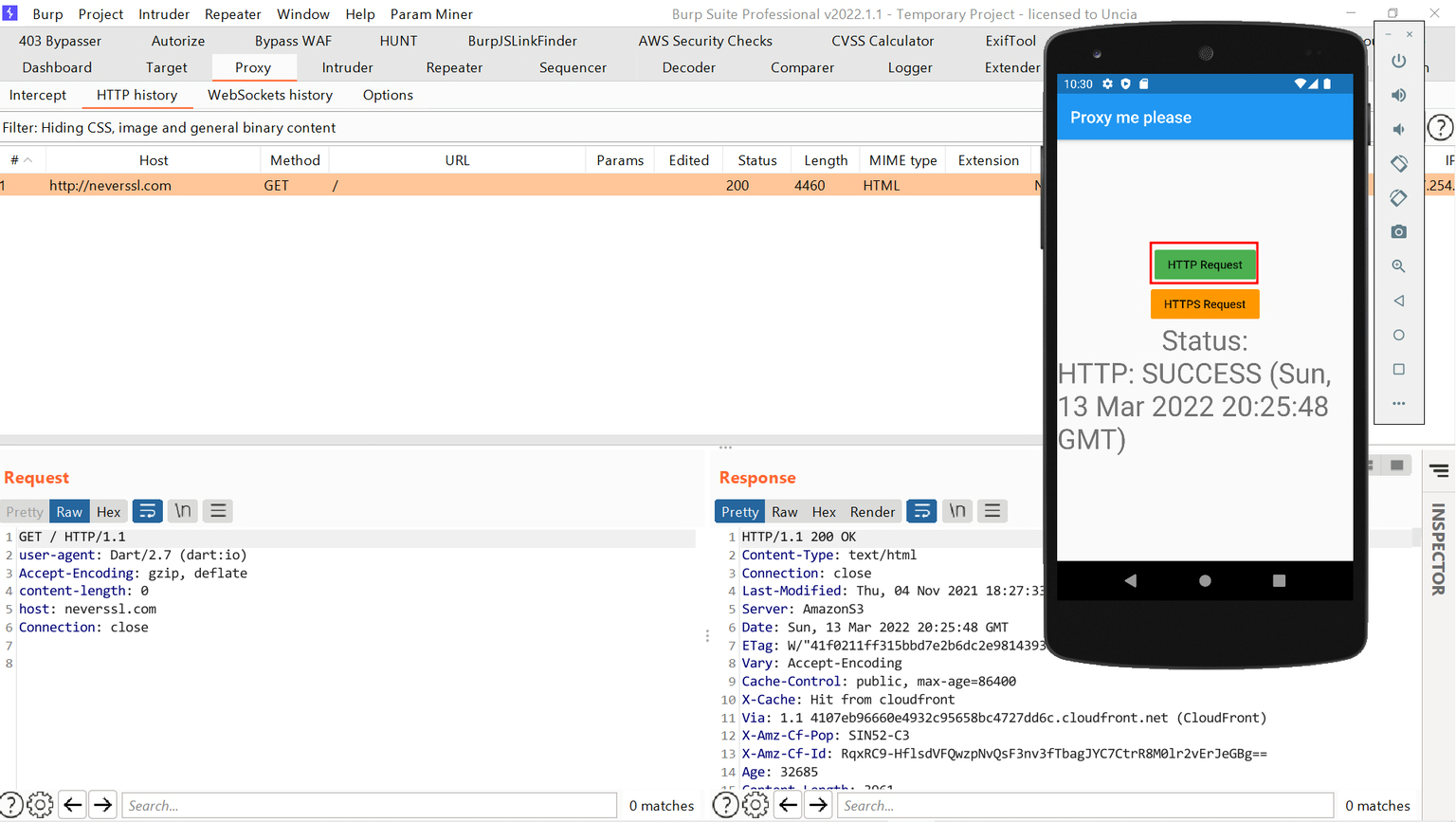
The traffic through the burpsuite and we will get success response.But If we click on HTTPS Request ,we will get error like this.
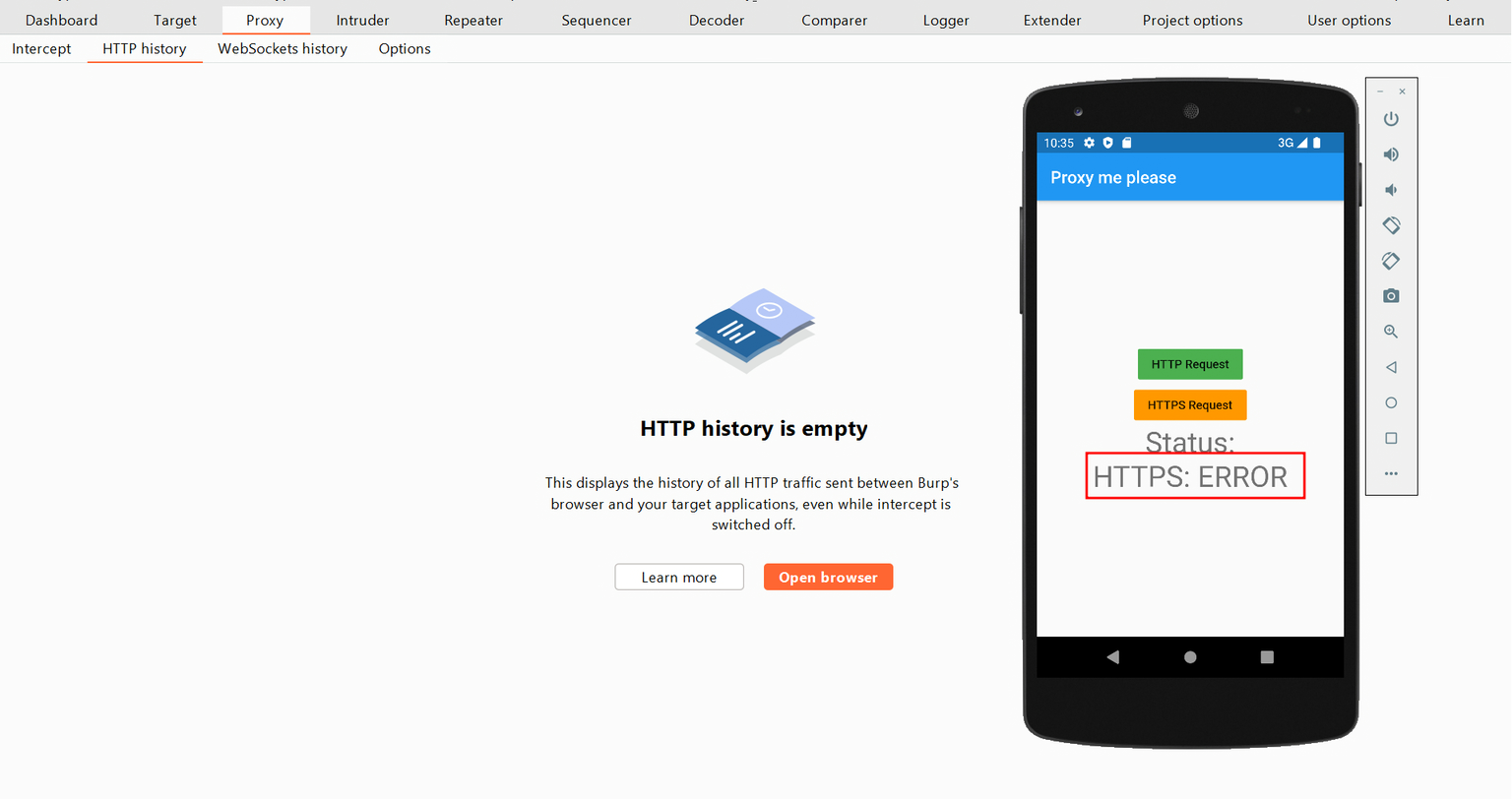
So, let’s bypass it using reflutter tool.
reflutter flutter-apps.apk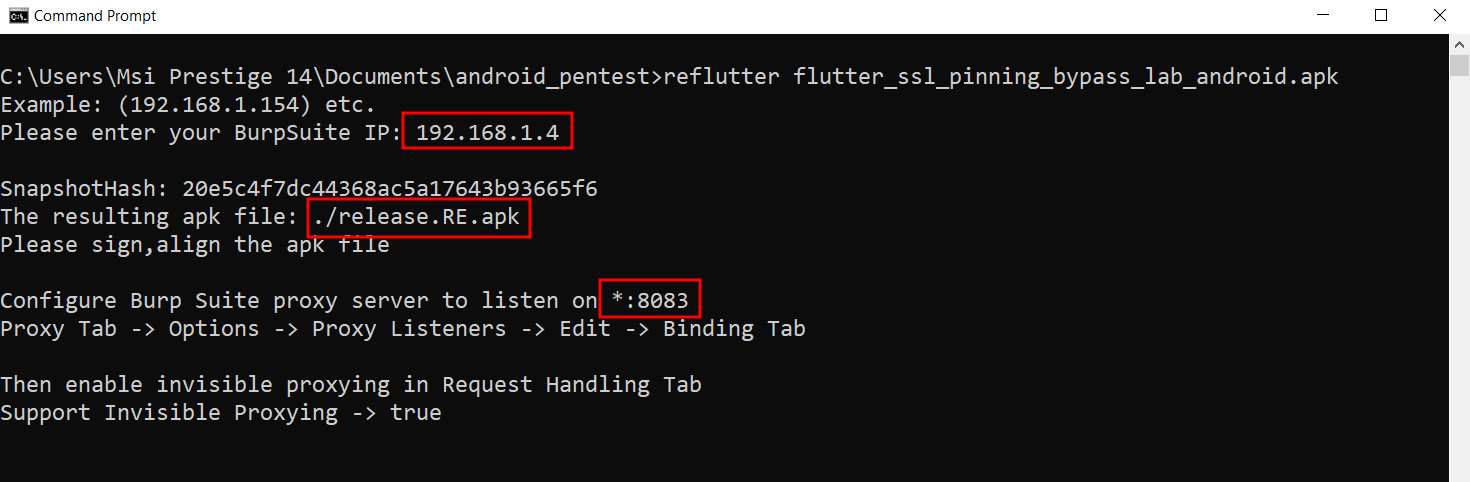
IP is our host machine IP which running burpsuite.
Now we will get release.RE.apk but this apk hasn’t signed yet. We have to sign manually.
I used uber-apk-signer in here. You can use your own method.
java -jar uber-apk-signer-1.2.1.jar --apk release.RE.apk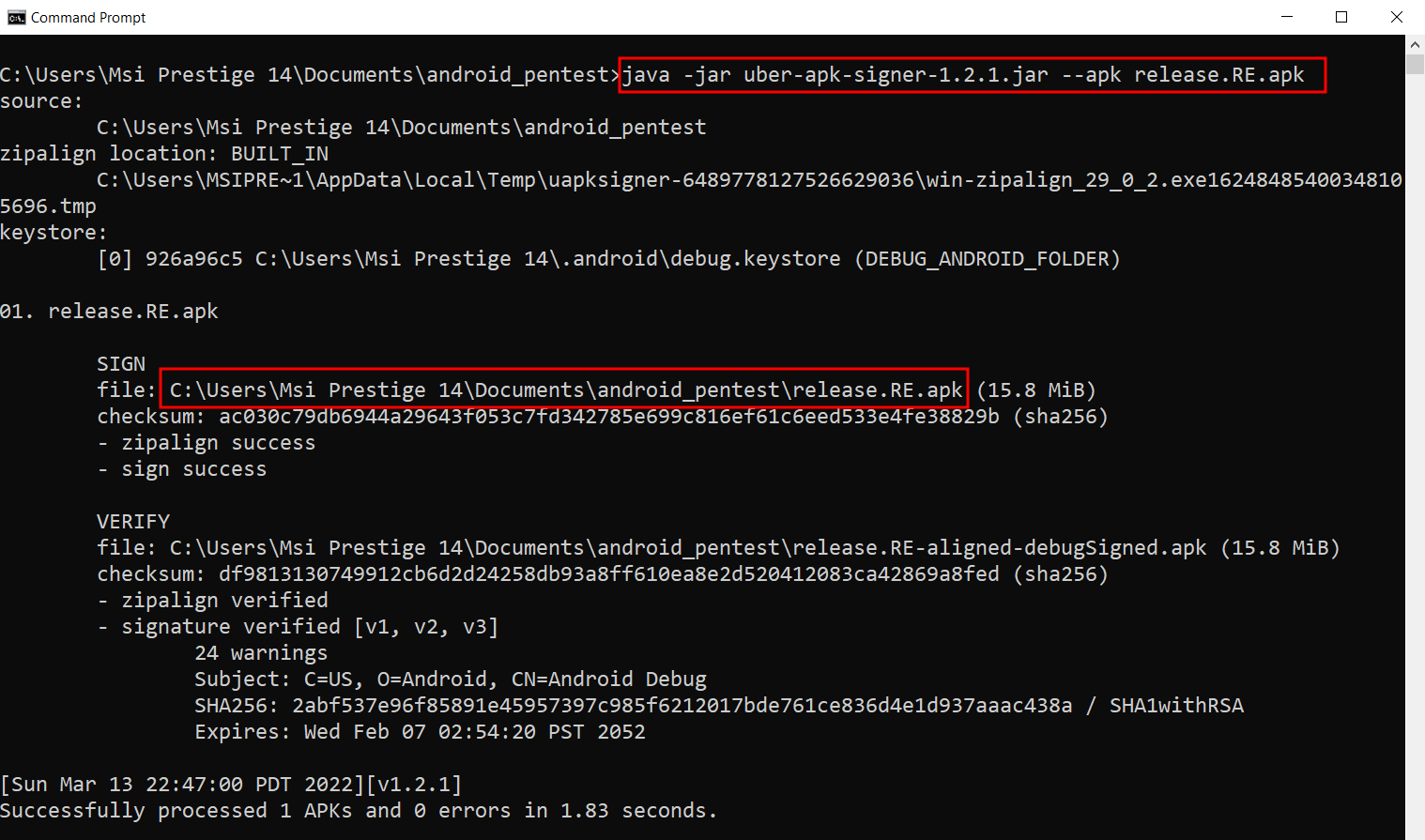
Now install signed apk in your device.
adb install release.RE-aligned-debugSigned.apk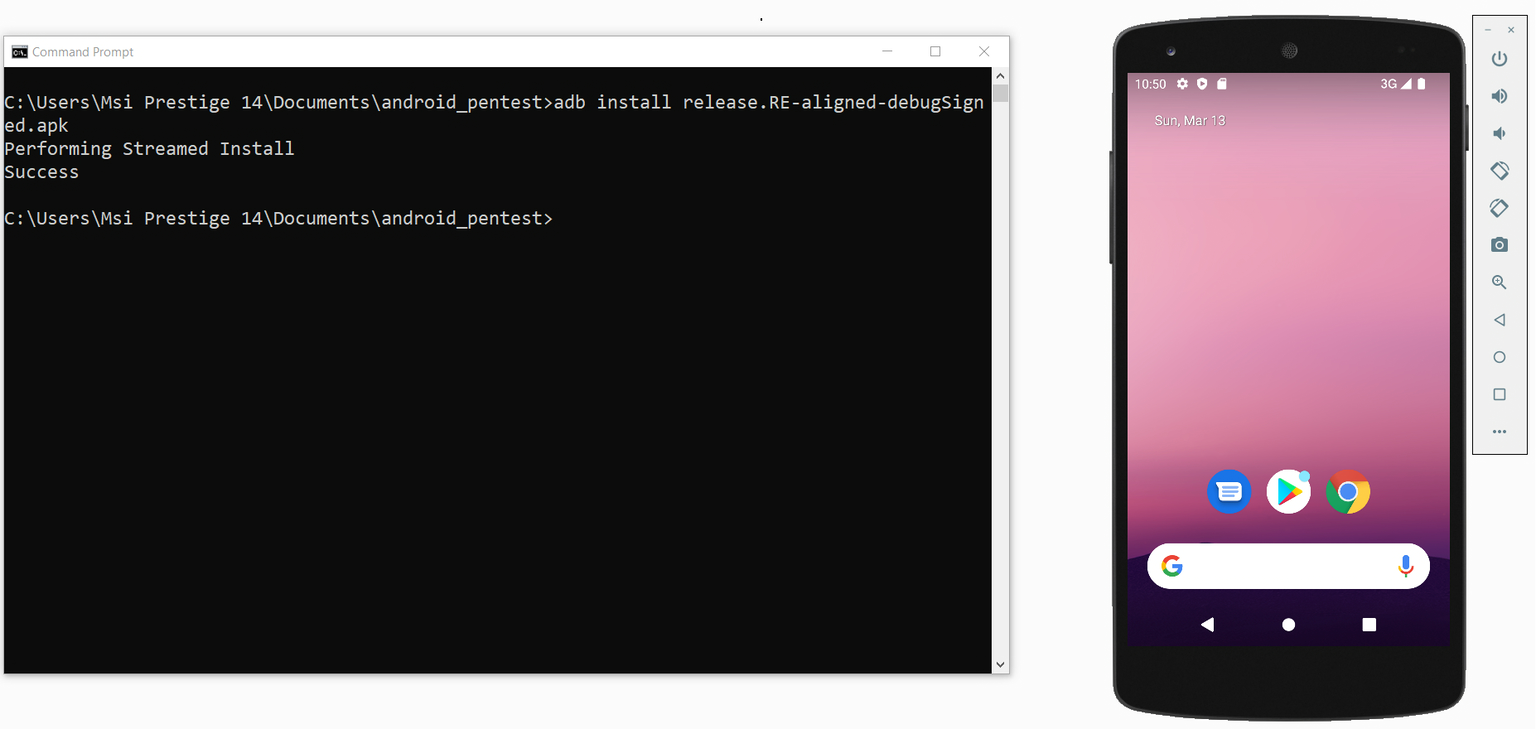
For the next step, we have to configure the proxy in burpsuite.
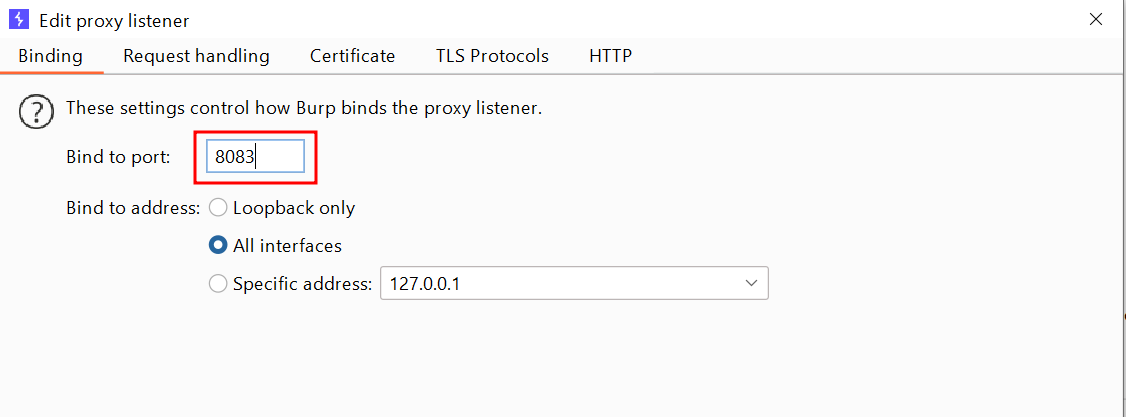
First, change port to 8083 because reFlutter set it by default.
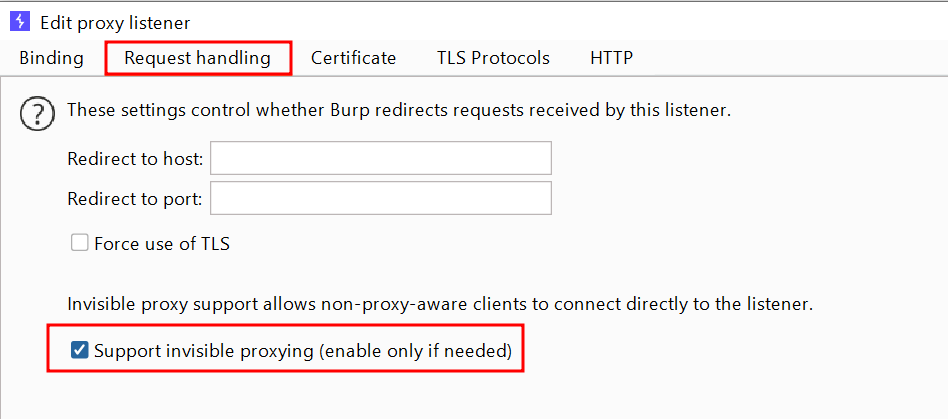
In Request handling tab, enable Support invisible proxying and click on OK.
Now open the new apk and click on HTTPS Request.
NOTEwe need to turn off proxy because reflutter is already modifed and set the proxy settings in the patched app.
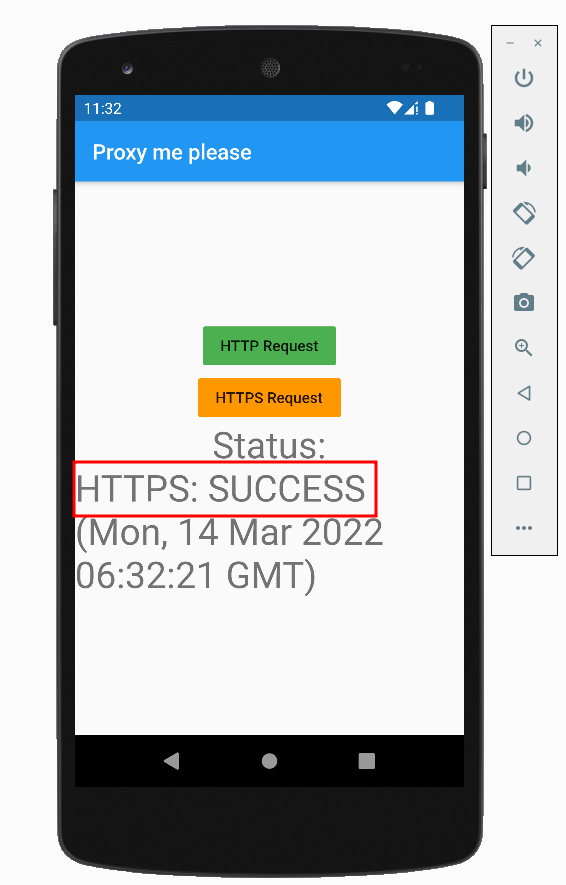
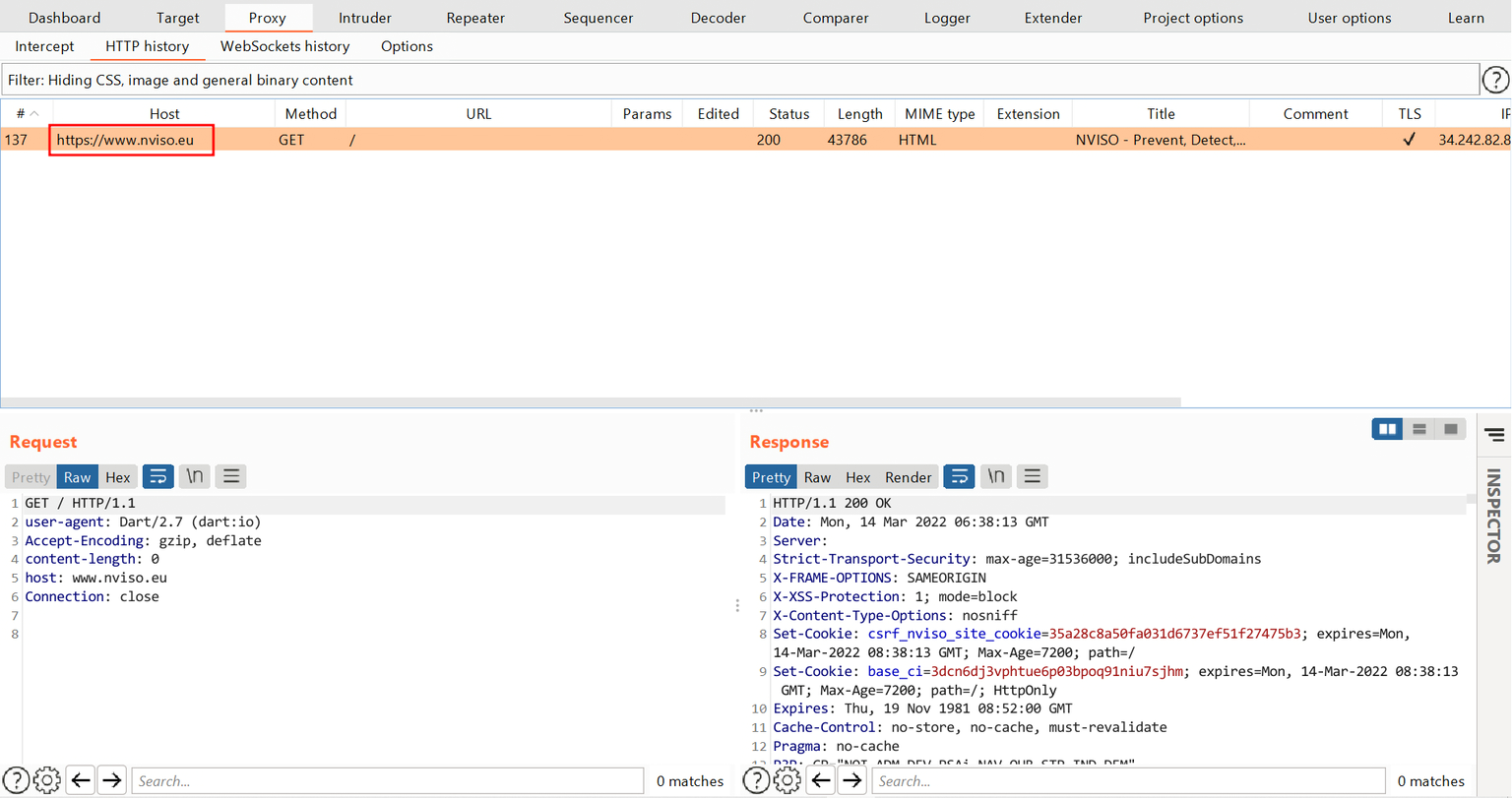
Now we can intercept the HTTPS traffic of the flutter based app by using reFlutter tool.
