Back in 2022, I didn’t have a job yet at that time. So I was just doing full time bug bounty hunting and got a couple of bounties from hackerone and zerocopter. One day I saw a fresh program in zerocopter by searching with google dorks, I think no one hunt it yet on this program except their internal pentest team.
There are no other subdomains and only one domain is in scope. So I quickly grab the link and make an account.
After creating account, I go to my profile and it look like this.
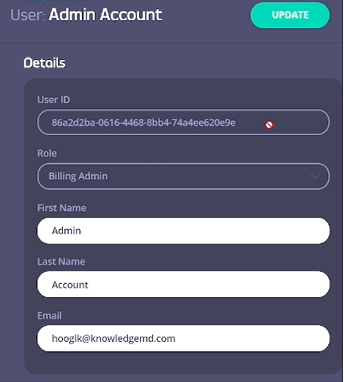
I noticed that we have our own userID, it look like unique ID. And we can edit our profile such as firstName, lastName and Email.
So I intercept edit profile endpoint with burp and the request look like this.
PUT /api/users/86a2d2ba-0616-4468-8bb4-74a4ee620e9e HTTP/2Host: account.cloud-ara.tyk.ioCookie: ---[snip]---Content-Length: 68Sec-Ch-Ua: " Not A;Brand";v="99", "Chromium";v="102", "Google Chrome";v="102"Accept: application/json, text/plain, */*Content-Type: application/jsonSec-Ch-Ua-Mobile: ?0User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/102.0.0.0 Safari/537.36Sec-Ch-Ua-Platform: "Windows"Origin: https://account.cloud-ara.tyk.ioSec-Fetch-Site: same-originSec-Fetch-Mode: corsSec-Fetch-Dest: emptyReferer: https://account.cloud-ara.tyk.io/account-admins/86a2d2ba-0616-4468-8bb4-74a4ee620e9eAccept-Encoding: gzip, deflateAccept-Language: en-US,en;q=0.9
{"firstName":"Member","lastName":"Account","email":"member@member.com"}By looking this request, the first thing in my mind was IDOR. So before thinking about possible or not as per their unique ID, I create another account and grab the userID.
And click on edit profile and intercept again with brup. Then I replaced with another userID with the current userID.The request will be like this.
Replace userID:
PUT /api/users/86a2d2ba-0616-4468-8bb4-74a4ee620e9e # hereRequest Body:
{"firstName":"Hacked","lastName":"Admin Account","email":"hacked@admin.com"}Fortunately, it was changed the name and email of another user’s account. To be honest, I really did not expect that cuz in their responsible disclosure page, they already mentioned that they have their own internal team to test their website. So this kind of bug should be aware.
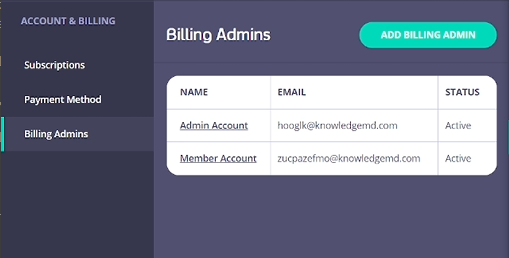
Now the problem is how can we get that kind of unique ID? Then I found one endpoint that disclosing that userID which in Billing Admins tab.
In this tab, we can invite another member. So after the user accepted our invite we can see like this.
If we click on member account, we can see their profile including their unquieID.
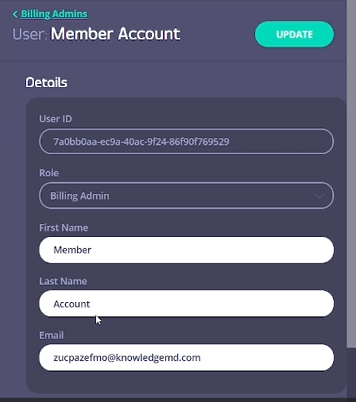
So to get the userID, the user must be in our team or otherwise we have to invite them. If we get their ID, we can change their email which will lead to account takeover. Then I quickly create the POC and report it. After one day, the issue has been verified and they reward me 4 digit bounty which I wasn’t expect xD.