I’ve never posted a CTF writeup before since I usually just keep my notes in CherryTree. But today, I finally decided to share one.
Chalenges Summary
- Cryptography - 4
- Misc - 4
- Forensics [3]
- OSINT [1]
- Web [1]
- Networking [1]
Let’s start with Cryptography
I could’ve sovled 4 challenges under cryto category.
Cryptography
1. BiG BrAiN (80)
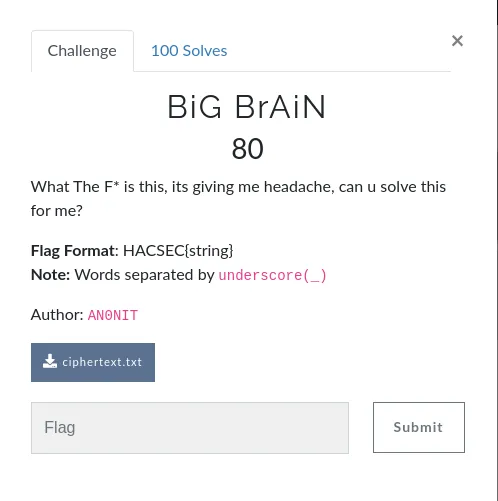
This is the content of ciphertext.txt file.

Obviously , It’s a brain fuck language ,so I decode it from Here and get the flag.

FLAGHACSEC{y3s_y0u_n33d_br4in_t0_Cr4Ck_Br4inf#ck}
2.ARE u SuRE(100)
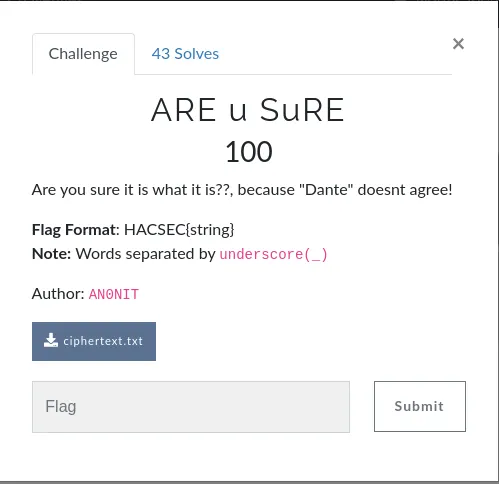
ciphertext.txt

My first thought was ASCII85, but it didn’t work. I have seen similar like this before in JohnHammond youtube video which mentioning about Malbolge.
Malbolge is an esoteric programming language created by Ben Olmstead in 1998, intentionally designed to be one of the most difficult to use.
Paste it in HERE , click on run program and we will get the flag.
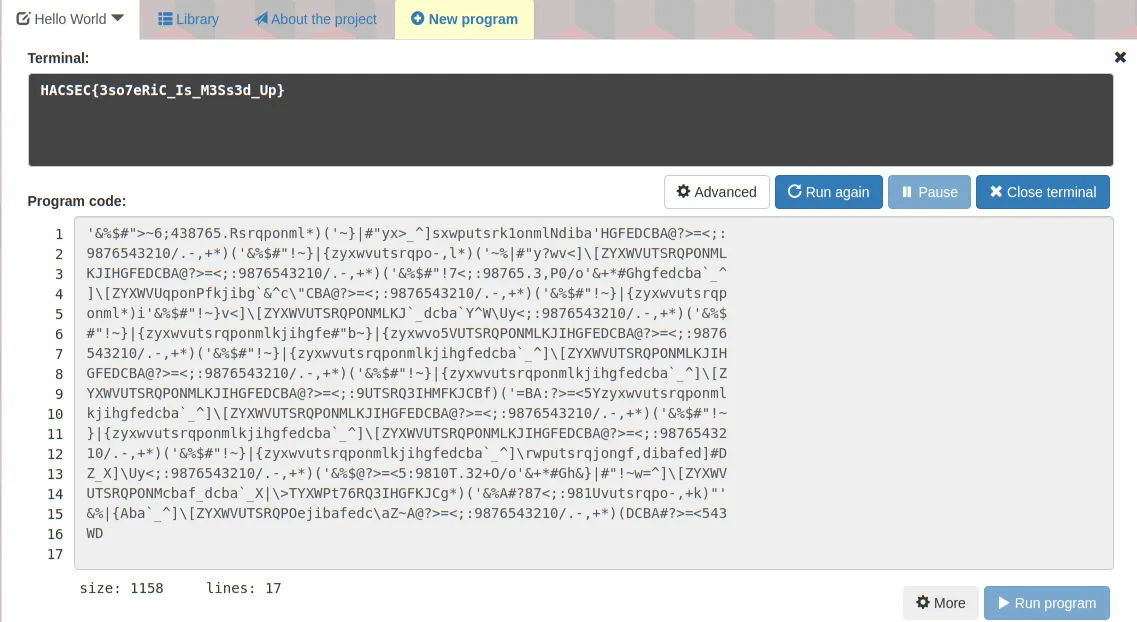
FLAGHACSEC{3so7eRiC_Is_M3Ss3d_Up}
3.Baby RSA(100)
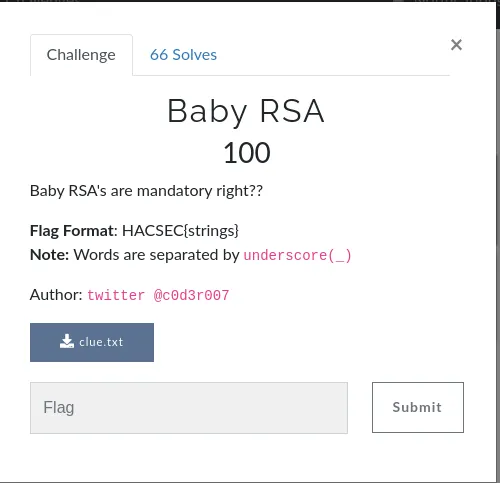
clue.txt
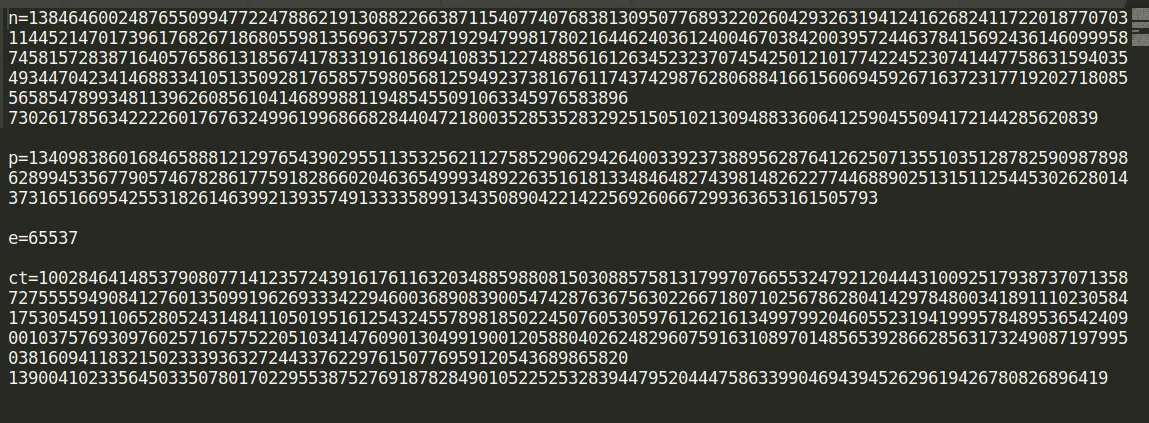
A clue.txt file was included RSA-encrypted text. Luckily, I’d already solved similar RSA challenges before, so I used my existing python script to solve it.
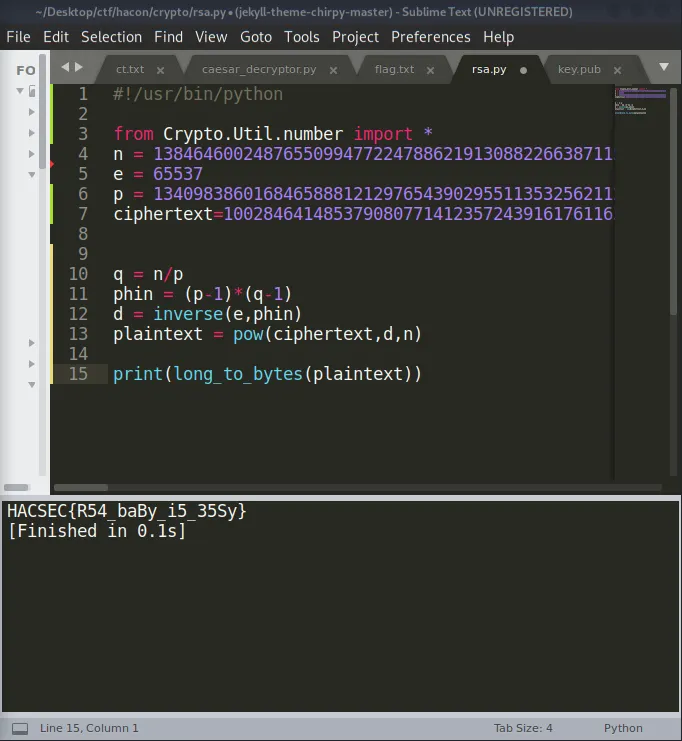
FLAGHACSEC{R54_baBy_i5_35Sy}
4.MIRROR MIRROR(100)

ct.txt
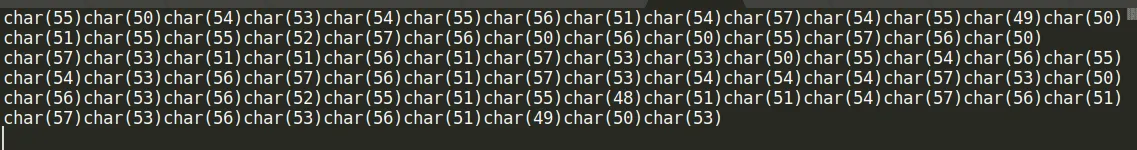
I removed chr() with sublime text and decode it with decimal to text

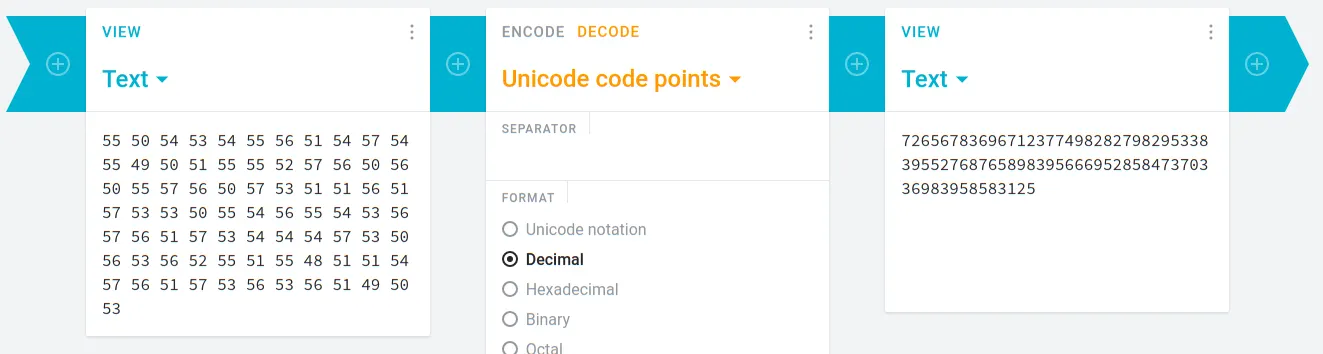
I got another numbers. I was confused a moment and then I thought it might be another decimal, so I splited it by space and decode it again.
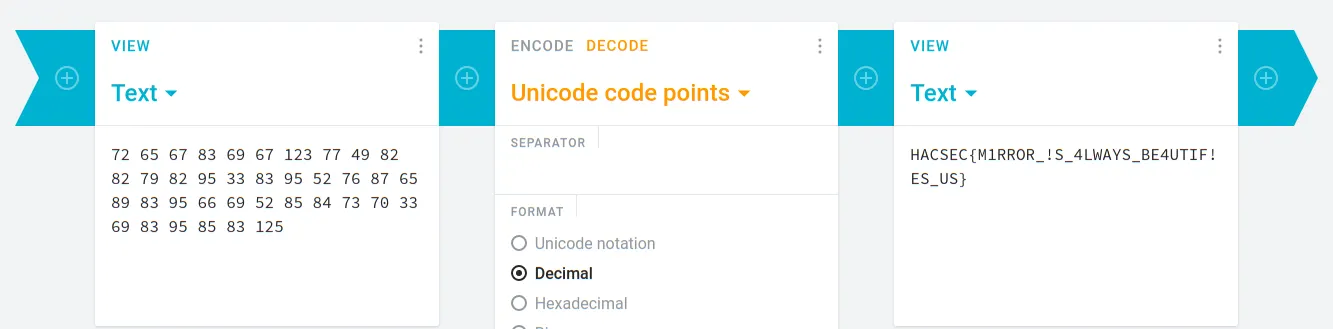
FLAGHACSEC{M1RROR_!S_4LWAYS_BE4UTIF!ES_US}
